Chapeta maintains two tiers of blocked Bash command patterns. Always-blocked patterns (fork bombs, raw device writes) are enforced in every mode including God Mode. Standard blocked patterns (rm -rf /, sudo, etc.) are enforced in Supervised, Balanced, and Autopilot modes but can be bypassed in God Mode. Both tiers are hardcoded in the app binary.
How It Works
- Before any command is sent to the shell, Chapeta checks it against both blocklist tiers.
- Always-blocked patterns (fork bombs, infinite background loops, raw device writes) are rejected in every mode.
- Standard blocked patterns (destructive filesystem ops, remote code execution, credential exfiltration) are rejected in all modes except God Mode.
- The AI receives an error message explaining why the command was blocked.
- The AI must find an alternative approach that does not use blocked patterns.
Benefits
- Prevents the most catastrophic possible commands.
- Works in every approval mode, including Autopilot.
- Hardcoded in the app binary. Cannot be circumvented by prompt injection.
- Covers destructive shell patterns before they ever run.
Tradeoffs
- Some legitimate commands may match blocked patterns.
- The blocklist is not configurable. You cannot add or remove patterns.
- Pattern matching is not a complete security solution. Novel attack vectors may not be covered.
FAQ
More Safety Features
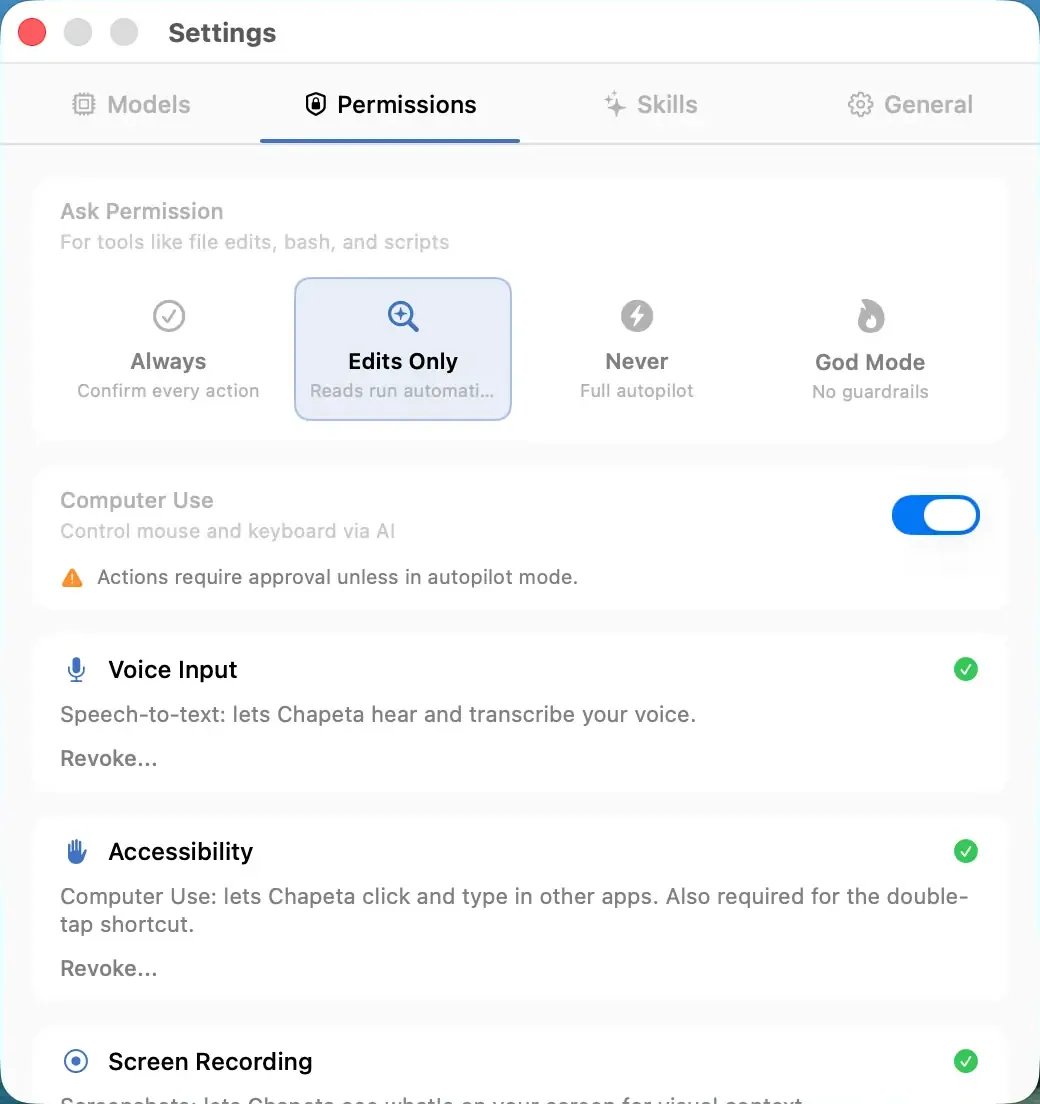
Supervised Mode
Approve every tool action before it runs. Zero surprises.
Balanced Mode
Safe actions auto-approve. Dangerous actions require confirmation.
Autopilot Mode
Full automatic execution. No approval prompts. Maximum speed.